'GothFerrari' Sentenced to 78 Months as Crypto Theft Moves Beyond Online Fraud
2026-05-07 18:21:00
## Ferro's sentence shows crypto theft can move from phishing to front doors

According to [Decrypt](https://decrypt.co/367066/hardware-wallet-thief-gets-78-months-in-prison-over-250m-crypto-heist), Marlon Ferro, a 20-year-old California man known online as "GothFerrari," was sentenced on May 6, 2026, to 78 months in federal prison for his role in a cryptocurrency theft enterprise that prosecutors said stole more than $250 million.
The headline number is the prison term, but the sharper issue is the attack pattern. The case connects three layers that crypto security discussions often treat separately: social engineering, hardware-wallet custody, and physical intrusion.

### Court record: sentencing, restitution, and supervision are already fixed
The [U.S. Attorney's Office for the District of Columbia](https://www.justice.gov/usao-dc/pr/gothferrari-sentenced-78-months-prison-role-massive-cryptocurrency-heist) said Ferro pleaded guilty on Oct. 17, 2025, to conspiracy to participate in a racketeer influenced and corrupt organization. Judge Colleen Kollar-Kotelly also ordered three years of supervised release and $2.5 million in restitution.
The enterprise, according to prosecutors, operated between late 2023 and early 2025. Its members handled database hacking, target identification, fraudulent calls, money laundering, and residential burglary. The core variable is role specialization: Ferro's assigned value inside that chain was not technical brilliance; it was the willingness to cross from remote pressure into a victim's home.
That distinction matters for risk analysis. A theft model built around named targets, addresses, and laundering channels behaves differently from a broad phishing campaign. If investigators can keep tying each role to a specific step in the chain, future cases may become easier to explain to courts and harder for participants to describe as isolated online conduct.
### Hardware-wallet security: the device moved the attack toward people and addresses
Hardware wallets are often discussed as a defense against remote compromise. This case shows the other side of that design. When a device cannot be reached online, the threat may move toward the person, the address, and the routines around storage. The risk boundary therefore is not only cryptographic; it is operational.
Prosecutors described two examples. In February 2024, Ferro traveled to Winnsboro, Texas, and stole a hardware wallet containing about 100 BTC, then valued at more than $5 million. Five months later, in New Mexico, he surveilled another residence and smashed a window with a brick while searching for hardware wallets.
## The legal focus is not just theft; it is a role inside a racketeering chain
The case matters because it frames crypto theft as an organized service model rather than a single online intrusion. The alleged enterprise used social engineering to pressure victims, hacking to seek access, and burglary when digital routes failed. That sequence is important: physical force was not separate from the cyber scheme, but a fallback inside it.
This is the structural difference from a typical exchange exploit. In an exploit, the technical path often carries most of the explanation. Here, the explanation depends on whether targeting, travel, burglary, and laundering can be read as one business process. That is why the legal framing is as important as the stolen-asset figure.
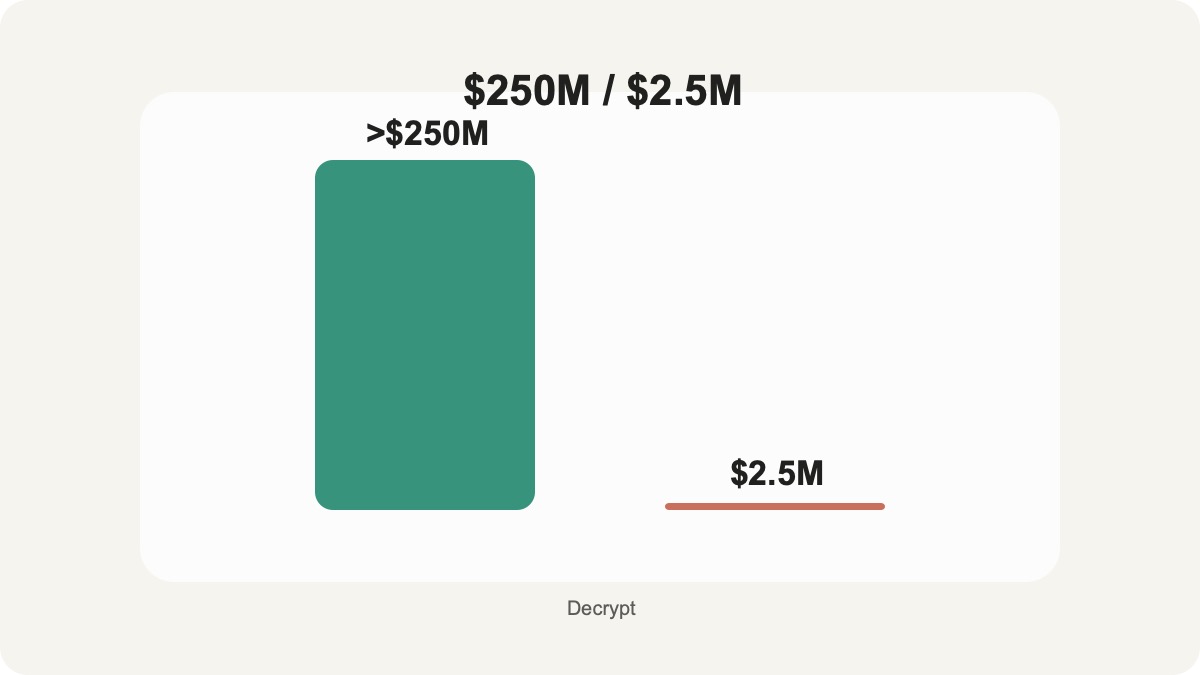
### Restitution separates personal conduct from enterprise scale
The $250 million figure describes the broader criminal enterprise. The $2.5 million restitution order is attached to Ferro's sentence. Keeping those numbers separate avoids overstating one defendant's direct obligation while preserving the scale of the alleged conspiracy.
#### The enterprise number explains the enforcement posture
A theft ring that crosses states, uses fraudulent IDs, launders proceeds through exchanges, and funds luxury spending gives prosecutors a stronger basis to describe the conduct as structured criminal activity. The racketeering plea reflects that framing.
#### The individual order points to a narrower court remedy
Restitution does not solve the full victim-loss problem. It does, however, show how courts can attach a concrete repayment figure to a participant whose role combined burglary and laundering rather than only coding or account takeover.
## Custody security now has to account for location, identity, and routine
The security lesson is not that hardware wallets failed. The device did what it is designed to do: make remote access harder. The failure point was the information trail around people believed to hold significant crypto assets.
### Institutional risk grows at handoff points
For companies, family offices, and service providers, the pressure point is often the handoff between digital controls and human operations: who knows wallet locations, who can identify signers, how travel or address data leaks, and whether emergency procedures assume only online threats.
### Individual holders face a privacy problem, not just a device problem
For individuals, the boundary is similar but more personal. Public identity, visible wealth signals, shipping records, old breaches, and predictable routines can turn a private key problem into a personal-safety problem. This case makes that connection visible without requiring a new theory of blockchain risk.
The next legal signal will come from related cases in the same network, not from the price of any asset. The useful verification framework has three parts: whether prosecutors keep naming the online targeting path, whether court records keep linking physical access to that path, and whether laundering infrastructure is described as a necessary bridge to spending. If those pieces stay connected, the case becomes a custody-security reference point rather than only another sentencing headline.
---
Author: Coinalx Editorial Team|First published: 2026-05-07 | Last updated: 2026-05-07
Source: [decrypt.co](https://decrypt.co/367066/hardware-wallet-thief-gets-78-months-in-prison-over-250m-crypto-heist)
DISCLAIMER:
1. All content on this website (including but not limited to articles, data, charts, and analyses) is for general informational purposes only and does not constitute any form of investment advice, trading recommendation, or financial guidance.
2. Cryptocurrencies and digital assets are subject to extreme price volatility and high investment risk; you may lose part or all of your principal. Past performance does not predict future results.
3. The information on this website is based on sources we believe to be reliable, but we do not guarantee its accuracy, completeness, or timeliness. Any investment decisions made based on this website’s information are at your own risk.
4. We strongly recommend that you conduct your own thorough research and consult an independent, licensed financial advisor before making any investment decisions.